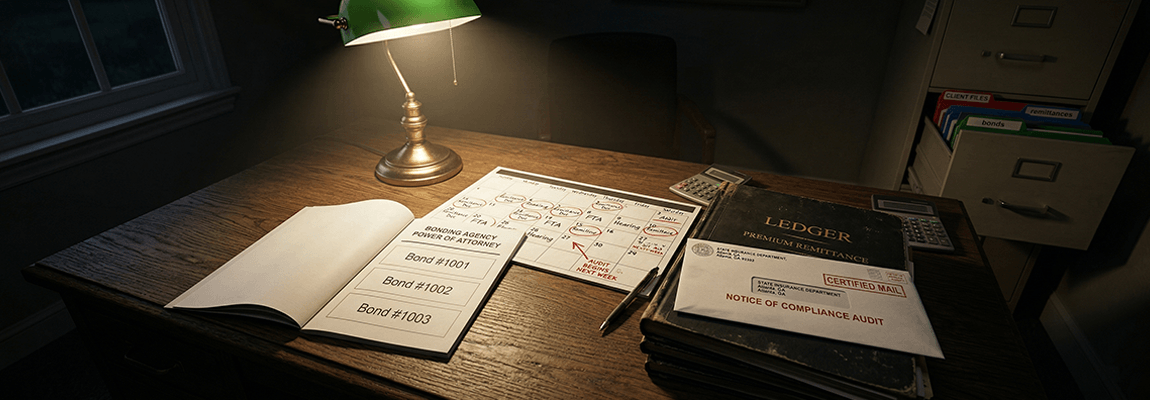
Bail agency compliance risk does not usually announce itself. It builds quietly, in filing cabinets that have not been audited, in remittance schedules that slipped by two weeks last quarter, in powers of attorney that were issued but never properly tracked. The financial lifecycle of a bail bond has regulatory checkpoints at every stage. Most agencies have never mapped them.
When the surety's loss control team calls, or a state insurance department examiner sends a records request, the agencies that survive the review intact are the ones that built their compliance systems before they were asked to prove them. The ones that scramble are the ones that assumed compliance was something that happened naturally when everyone was doing their jobs. It is not. Compliance is a system, and systems have to be designed.
Key Takeaways
- Most bail agency compliance failures are not intentional: they are structural gaps in record-keeping, POA management, and remittance timing that accumulate silently until a regulator or surety forces the conversation.
- Power of attorney accountability is the highest-risk compliance area for most agencies: a single misused, unaccounted, or improperly voided POA can trigger surety termination regardless of the agency's overall performance record.
- Premium remittance timing is a contractual obligation, not a billing preference: late remittances, even when the premium has been collected, create surety liability exposure and can trigger account review or termination.
- State filing deadline requirements vary significantly and change without reliable notice: agencies that rely on memory rather than a compliance calendar consistently miss deadlines that produce administrative fines or license jeopardy.
- Audit-ready documentation is the operational output that distinguishes agencies that survive regulatory review from those that do not: the regulator's question is never what happened; it is always what you can prove.
What Compliance Actually Means in a Bail Agency
Compliance in the bail context operates across three distinct regulatory relationships simultaneously: the state insurance department, which licenses the bail agent and oversees premium practices; the surety company, which issues the powers of attorney and sets contractual operating standards; and the courts, which have their own filing and bond execution requirements. Each relationship has its own documentation standards, timelines, and failure modes.
Most agency owners understand this in principle. Fewer have translated that understanding into operational systems that produce audit-ready documentation as a natural output of daily work. The gap between knowing what compliance requires and having proof that you did it is where most enforcement actions originate.
The surety relationship is the compliance axis that carries the most concentrated operational risk: a surety termination ends the agency's ability to write bonds far more immediately than any state administrative fine. Understanding which compliance failures trigger which surety responses is the first step in prioritizing where to build controls.
The POA Accountability Gap
Power of attorney documents are the instrument by which a surety authorizes a bail agent to execute bonds on their behalf. Each POA has a face amount, a bond number, and a corresponding obligation that attaches to the surety the moment the agent signs it. The surety's exposure is real the moment the POA is used. The agent's obligation to account for every POA issued to them is equally real from the moment of receipt.
POA accountability failures come in three forms, all of them common and all of them serious.
Inventory tracking gaps
Many agencies receive POA booklets from their surety and do not maintain a real-time log of which POAs have been used, which are in inventory, and which have been voided. When an examiner asks for a reconciliation, the agency that cannot produce one, or produces one that does not match the surety's records, is immediately in a difficult position regardless of intent. The surety's records and the agency's records will be compared. Discrepancies generate questions the agency cannot answer without documentation.
Voiding procedure failures
A POA that is not used must be voided according to the surety's specific procedure: typically, the original document is returned to the surety with a written void notation, and the agency retains a copy with a matching notation. Agencies that void POAs informally, discarding documents or noting voids only in internal software without returning originals, create a gap in the paper trail that is difficult to explain during a loss control review. The surety's position is that any unaccounted POA is a potential unrecorded liability. They are not wrong.
Agent departure protocols
When a licensed bail agent leaves an agency, the POAs issued to them in their name must be recovered, voided, and returned. This step is missed with surprising frequency, particularly in acrimonious departures, because the departing agent holds the physical documents and the agency owner is focused on other aspects of the transition. An unrecovered POA in the hands of a former agent who is no longer authorized to write bonds on that surety's paper is one of the highest individual compliance risks an agency can carry. The operational handoff protocol for departing agents needs to include POA recovery as a non-negotiable step, not an afterthought.
Record-Keeping Failures That Produce Fine Risk
State insurance departments require bail agencies to maintain records of every bond written, every premium collected, and every disbursement made, typically for a minimum of five years, though the specific requirement varies by state and some states require longer retention periods. The practical standard to hold is: keep everything, and keep it in a format that can be produced on short notice.
The most common record-keeping failures are not missing records, they are incomplete records. A bond file that contains the application and the executed bond but lacks the premium receipt, the indemnity agreement, and the collateral documentation is incomplete. An incomplete file is not a compliant file. An examiner reviewing a sample of files where a significant percentage are incomplete will generate a finding even if no actual compliance violation occurred. The finding becomes a matter of administrative record regardless of outcome.
Digital versus physical records
Most agencies have moved to digital management systems for active bonds. The compliance risk is in the transition: physical records from prior years that were never digitized, digital records stored in systems that are no longer accessible after a software change, and hybrid filing systems where some documents are in the agency's software and others are in a filing cabinet, with no systematic index connecting them. An examiner who asks for a complete bond file for a specific bond number should be able to receive that file in a format the agency can produce in minutes, not hours.
Premium receipt documentation
Every premium payment, including each installment on a payment plan, requires a receipt. That receipt must be issued at the time of payment and retained as part of the bond file. The risk profile of a bond and its premium collection history are connected: the payment plan file that shows consistent on-time receipts is also a bond file that shows a compliant transaction. Agencies that issue receipts informally or inconsistently create gaps that are difficult to retroactively close during a records review.
Premium Remittance Timing: A Contractual Obligation, Not a Billing Preference
The agency's agreement with its surety specifies a remittance schedule: typically, the agency is required to remit the surety's portion of collected premiums within a defined window, often thirty to sixty days from collection, depending on the agreement terms. This is not a billing preference. It is a contractual obligation with consequences for breach.
Late remittances are one of the most common sources of surety warning letters and account reviews. The reason they are common is structural: the agency collects the full premium, deposits it, and then must separately identify and transfer the surety's portion on a schedule that requires discipline to maintain. When cash flow is tight, agencies delay remittances. When the backlog accumulates, the surety's accounting records and the agency's records diverge. When the discrepancy is discovered, the conversation that follows is not comfortable.
Float is not yours to use
The most important reframe for agency owners managing cash flow is this: the surety's portion of collected premiums is not your money once collected. It is a liability on your books from the moment the premium is received. Using that float to cover operational expenses and intending to remit later is the same financial structure as using client trust funds for operating costs: it creates a gap between what you owe and what you have, and that gap grows faster than most owners anticipate when business is slow.
The post-execution revenue management framework is built around treating each premium component as a separate obligation from collection. The surety's portion is earmarked and remitted on schedule. The agency's portion funds operations. This separation is not complicated to implement, and it eliminates the remittance timing problem before it starts.
State Filing Deadlines: The Calendar Risk Most Agencies Do Not Track
Every state has specific filing requirements for bail agencies operating within its jurisdiction: license renewal deadlines, continuing education completion requirements, bond forfeiture response windows, and periodic financial reporting obligations that vary by state and, in many cases, by county. These deadlines are not announced by reminders from the state. They exist in the regulatory code, and the agency is responsible for knowing and meeting them regardless of whether a notice was received.
The failure mode is predictable: an agency operating in multiple counties, or managing a high volume of active bonds, misses a forfeiture response deadline by a few days because the deadline was tracked informally. The court enters summary judgment. The summary judgment process that follows is expensive, time-consuming, and often involves surety liability that would have been avoided by a timely response. The entire sequence traces back to a calendar management failure, not an underwriting failure or a fugitive recovery failure.
Forfeiture response windows are the highest-stakes deadline
When a defendant fails to appear, the court issues a forfeiture notice. The bail agent and surety have a defined window, typically 180 days but varying significantly by state, to respond: either by producing the defendant, providing a valid legal excuse for the absence, or negotiating a remission. Missing the response deadline converts a manageable forfeiture situation into a surety bond enforcement action that is significantly harder to resolve. Every forfeiture notice that arrives at the agency needs to be date-stamped, entered into a tracking system, and assigned a response deadline before the file is handled for any other purpose.
License renewal and CE requirements
State bail agent license renewal deadlines and continuing education hour requirements are among the most commonly missed administrative deadlines. They are missed not because agents do not know they exist, but because they are annual or biennial requirements that do not feel urgent until they are. An agent whose license lapses, even for a period of days, cannot legally write bonds during the lapse period. Any bonds written during a lapsed license period are a compliance exposure for the agency, the agent, and potentially the surety.
The Surety Relationship Risk: How Compliance Failures Escalate
Sureties monitor their appointed agents through a combination of loss ratio review, remittance reconciliation, POA accounting, and periodic loss control audits. The escalation sequence typically follows a predictable path: a warning letter identifying a specific deficiency, a requirement for a written response and corrective action plan, an enhanced monitoring period with more frequent reporting requirements, and, if the deficiency continues or additional issues surface, termination of the appointment.
What most agency owners do not fully appreciate is that the surety's tolerance threshold for compliance failures is lower than their tolerance for loss ratio problems. A surety will work with an agency through a difficult loss period if the agency's documentation and process compliance are solid. They have much less patience for an agency that cannot account for its POAs, is consistently late on remittances, or has record-keeping gaps that make a loss control audit unproductive.
The compliance failure signals a management and process problem. The loss ratio signals a market or underwriting problem. Sureties believe they can help with underwriting. They cannot fix an agency that does not operate with basic administrative discipline. That distinction shapes how compliance failures are treated relative to performance problems: compliance issues escalate faster to termination.
Building a Compliance System That Works Before You Need It
The practical components of an agency compliance system are not complex. The agencies that build them well share a few characteristics: they treat compliance as a standing operational function, not a reactive response to regulatory inquiry; they assign explicit ownership for each compliance area rather than assuming it will be covered collectively; and they generate documentation as a natural output of daily operations rather than reconstructing it for audits.
A functional compliance calendar for a single-state bail agency should include, at minimum: monthly POA reconciliation against the surety's records; a remittance schedule tied to the agency agreement's required timing, with the surety portion tracked as a separate liability from the moment of collection; a forfeiture response tracker with deadline alerts set at thirty, sixty, and ninety days before each response window closes; and annual reminders for license renewal and continuing education deadlines, set ninety days out to allow adequate lead time.
For agencies operating across multiple states or counties, the calendar becomes more complex but the principle does not change: every compliance obligation needs an owner, a deadline in a system that surfaces it before it is urgent, and a documentation standard that produces a paper trail as the work is done. The question a regulator or surety examiner will ask is not whether your agency intended to be compliant. It is whether your agency can prove that it was. The gap between intention and proof is where enforcement actions live, and where agency compliance systems either earn their value or fail to exist at all.
IntelliBail's compliance tracking module is built around this operational model: deadline calendars, POA reconciliation tools, and remittance tracking integrated into the agency's daily workflow so that compliance documentation generates itself rather than requiring a separate administrative effort to produce.
Compliance blind spots close fastest when they have a system behind them, not just awareness of them. IntelliBail's compliance module surfaces deadline exposure, tracks POA reconciliation, and integrates remittance workflows so your paper trail builds itself.
See how IntelliBail handles compliance →